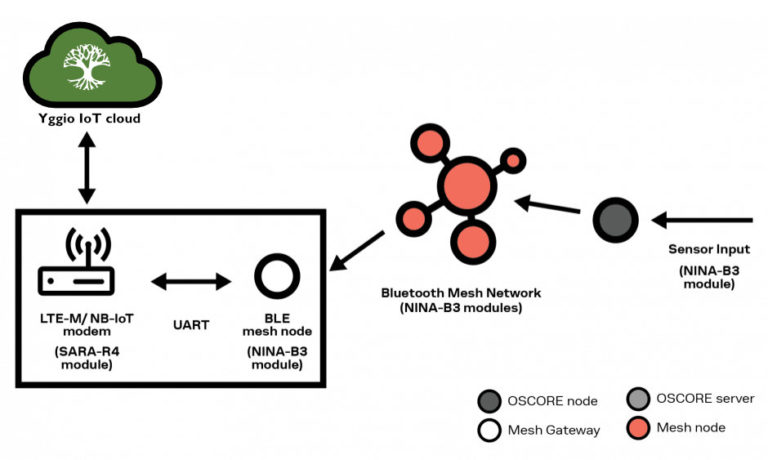
The goal of the project is to bring the latest IoT security standards into reality and to demonstrate it on a real use case from the smart public spaces project, the smart city network.
We have implemented and shown end-to-end encrypted data transfer from a sensor via public networks to Our Yggio IoT platform in the cloud, without data exposure that would act as a threat to data security.
Technologies
- Bluetooth Mesh (U-Blox)
- NB-IoT
- CoAP – Constrained Application Protocol
- OSCORE end-to-end encryption for constrained environments (IETF standard by RISE and Ericsson)
- Yggio IoT integration platform (Sensative)
Project managed by Mobile Heights in Lund with financing from Vinnova.
The details
IoT is used in a wide range of Smart City and Smart Building applications, where sensors and devices usually are small, cheap, and optimized for low power consumption and long battery life. These constraining factors, in combination with the mix of different standards and technologies deployed, makes security a real challenge. To address this, there is a new end-to-end encryption protocol standard; OCSORE – Object Security for Constrained RESTful Environments.
Defined by IETF (Internet Engineering Task Force), OSCORE brings some much-needed advantages:
- OSCORE encrypts only the data part of the payload, thus decreasing security overhead and increasing bandwidth usage and battery lifetime of the device. It also means that address information etc. is available for a transporting node without the need for decrypting the message.
- OSCORE replaces the key negotiation process, which is too resource-intensive for most constrained devices, by using pre‑shared keys.’
- Encrypted OSCORE messages can be as small as 11‑13 bytes, significantly smaller than most of the IoT security protocols used today, making OSCORE a suitable security option for constrained IoT nodes.